If you think the piracy and hijacking in the Gulf of Aden is dead now, you need to think again.
Yes, it has declined considerably but it still exists. And the pirates are looking for a window to strike again.
Blaming illegal fishing trade in Somalian waters, Somalis are considering the piracy again.
The recent hijacking incident in this area was as early as in March 2017.
On 13 March 2017, M/V Aris 13 came under attack from two skiffs and was taken hostage.
When sailing in these areas, we cannot let our guards down.
Good news is that with little preparation and by following the developed guidelines, the risk reduces considerably.
In this post, we will discuss the entire procedures of transit through this high-risk area.
But before we begin, let us understand these terms.
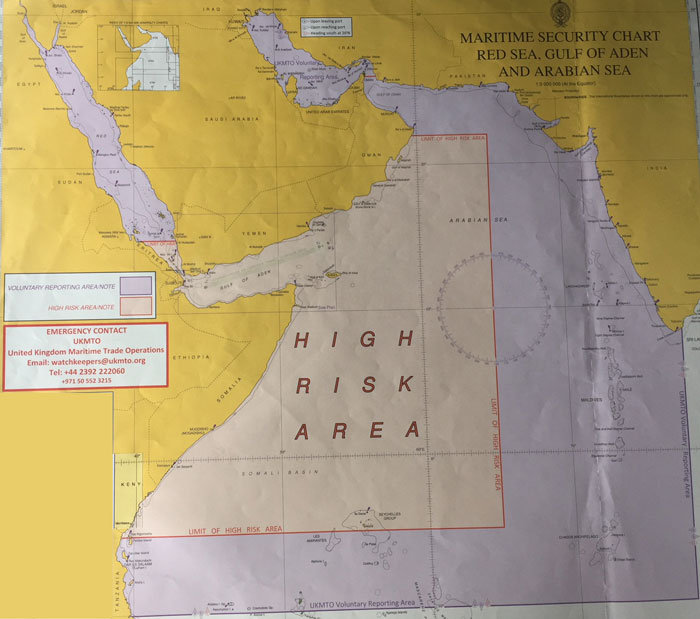
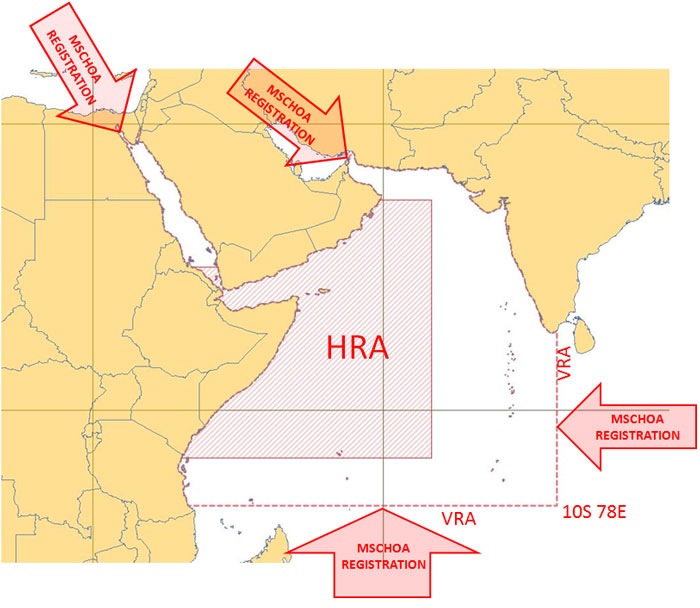
High-Risk area
The high-risk area has been designated based on the pirate’s activities and areas where most of the attack took place.
This is the area where it is considered that there is a higher risk of piracy.
This high-risk area is bounded by
- In the Red sea: Area south of Latitude 15 N
- In the Gulf of Oman: Area south of Latitude 22 N
- Eastern Limit: Area west of Longitude 65 E
- Southern Limit: Area North of Latitude 5 N
The Admiralty chart Q6099 is the guidance chart for these areas and must be on board before transit to the high-risk area.
The chart shows the clear picture of the area designated as High-risk area.
Voluntary reporting Area
Apart from HRA, UKMTO has set a voluntary reporting area where vessels are encouraged to report their activities.
This area can be seen as purple color in the Admiralty chart Q6099.
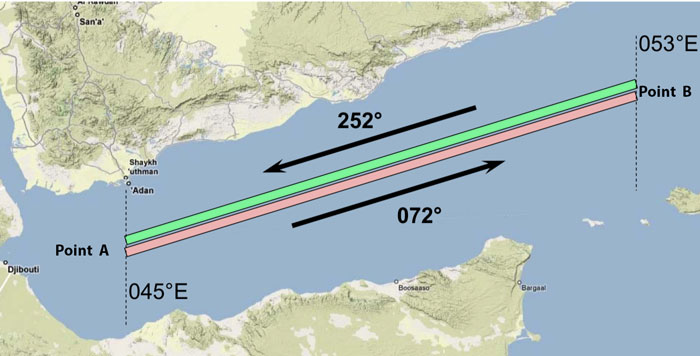
Internationally Recommended Transit Corridor (IRTC)
The area near the Gulf of Aden is the most crucial area when it comes to the Somalian piracy.
Most of the naval and Military forces focus on this area.
But this is still a large area and the resources are scarce.
To allow the Naval and military forces to concentrate on a comparatively smaller area, a transit corridor has been identified.
Ships are strongly advised to use this corridor to pass the Gulf of Aden.
The use of this area to transit gulf of Aden was also endorsed by the IMO’s sub-committee on navigation.
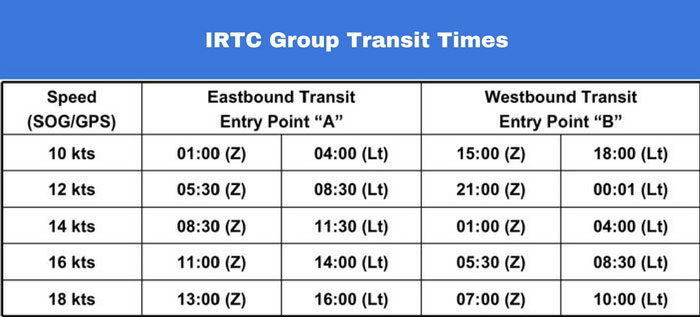
A group transit schedule has also been developed for this area based on the ship’s transit speed.
These timings are the recommendations. Of course, no one would like to delay the ship for 16-18 Hours to transit in these timings.
But if we can arrive the IRTC on these timings with just a couple of hours of delay, we must follow these transit timings.
The group transit through IRTC is not a convoy.
There will not be any naval escort ships either. The corridor just provides the security forces a defined area to concentrate upon.
When we arrive in this area, we must not wait for anyone in this area even if we do not see any other ship or warships.
Reporting Part of Gulf of Aden crossing
When we are transiting this high-risk area, there are lots of reporting that we need to make.
We must comply with all these reporting.
Let us see what all reportings we need to make.
1. Reporting to the hull insurance company (if required)
Most of the Hull & Machinery insurance companies would want to be notified if the ship intends to cross the HRA.
If so, follow the company’s instructions to notify the H&M insurer. The initial notification may be required well before the vessel’s entry into the high-risk area.
Some H&M insurers may need to be notified 48 hours prior entering HRA, other may need 7 days notice.
These instructions must be followed to avoid losing on any damage claims during the vessel’s transit through HRA.
2. Register the vessel with MSCHOA
Before entering the VRA, the vessel must register the vessel to the MSC-HOA.
What is MSCHOA?
The Maritime security center – Horn of Africa (MSCHOA) is the planning in coordinating center for EU Naval Forces (EUNAVFOR).
The MSCHOA collects the data from the ships and has that available to the naval security forces when required in case of rescue or providing help to the ships.
But, MSCHOA needs to have the ship’s voyage data for it to be able to share it with naval forces.
The vessel is required to send this data to the MSCHOA as a process to register the vessel.
To register with MSCHOA, the vessel needs to fill and send the MSCHOA registration form to the email postmaster@mschoa.org
After successful registration, the vessel will receive an email as the response to the vessel’s registration with MSCHOA.
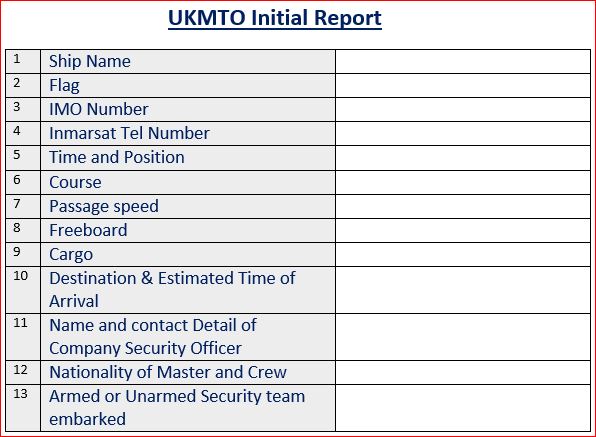
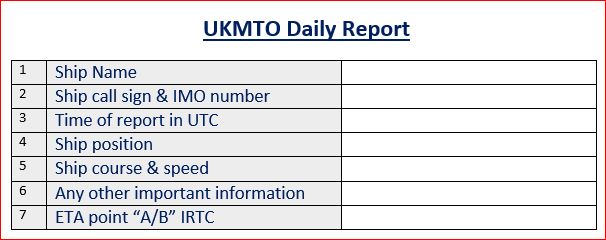
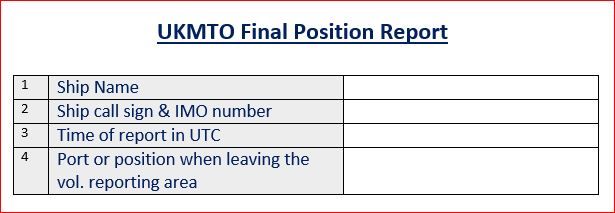
3. Report to UKMTO
The United Kingdom Marine Trade Operations (UKMTO) acts as an information bridge between international maritime trade and the security forces.
When vessel enters the voluntary reporting area, an initial report needs to be sent to the UKMTO.
Thereafter vessel needs to send the daily position updates at 0800 Hrs UTC.
Any suspicious activity or attack on the ship need to be reported to UKMTO. For this purpose, it is advisable to have the contact details of the UKMTO ready near the communication console of the ship.
Finally, upon exit from the high-risk area, vessel need to send the final report to UKMTO.
Prepare the vessel for transit
The most important part of Gulf of Aden transit is preparing the vessel. Before the vessel enters the high-risk area, the ship needs to be ready in all respect.
Vessel’s preparedness can be divided into three parts
- Preparedness of the ship to deter boarding
- Preparedness of the ship’s Citadel
- Preparedness of the crew to detect and respond to the security threat
1. Preparedness of the ship to deter boarding
The 4th edition of best management practices for protection against Somalia based piracy (BMP4) gives detailed instructions on deploying the barrier to deter boarding of the pirates.
This along with the company’s circulars and SSP should be referred to deploy the available barriers.
These barriers include
- Fixing the razor wires along the ship’s side.
- Water-jet guns on the ship side
- Spikes on the ship side
Some ships may even have the electric fencing along the ship side which can give a non-lethal electric shock.
Even if there is no electric fencing, BMP-4 suggests placing this placards along the ship’s side on razor wires.
This warning sign is in Somalian language stating “Danger High Voltage electric Barrier”.
Apart from the ship side, the barriers need to be there around accommodation area.
The idea is to avoid the pirates to get into accommodation for as long as possible.
For this reason, the access ladders to each of the outer accommodation ladders are fenced with razor wires.
Some ships even remove the ladders on the outer accommodation decks by removing the bolts with which it is fixed.
Whatever ways are provided in the ship security plan and available on board must be used.
All possible arrangements must be in place to deter pirate’s boarding the vessel and when boarded to deter them to get inside the accommodation and wheelhouse area.
Apart from the access barriers, ship security alarm system must be tested before entry into the high-risk area.
Check the company’s requirement for testing of SSAS.
2. Preparedness of the ship’s Citadel
The concept of the citadel is one of the most effective anti-piracy measure used since Somalia piracy surfaced.
Why?
The pirates invent new ways to break the barriers installed to deter their boarding.
For example, for the razor wire, they just fix a hook with a rope. Another end of the rope has some heavy weight attached to it.
They throw the weight end into the water. This takes some part of the razor wire down along with the weight.
This part is enough for the pirates to board the vessel.
But even when the pirates have boarded the vessel, there is still hope of getting rescued. Only if everyone hides in the Citadel.
What is citadel?
The dictionary meaning of citadel is
a strong castle in or near a city, where people can shelter from danger, especially during a war
With respect to ship security, usually engine room is designated as Citadel.
But to be called a citadel, it needs to have few basic things for the crew to survive in it for few days.
There need to be
- Water and food for the crew to survive for few days
- Few Blankets
- Iridium satellite phone to make contact with company security officer and/or Naval forces
- Strengthened entry points to not to allow easy access to the pirates
Few ships will also have CCTV cameras installed at various key locations with the viewing screen in the citadel.
This allows the crew in Citadel to monitor the pirate activities on the ship while they have locked themselves in the Citadel.
The content and equipments of the citadel must be checked before arrival into the high-risk area and it needs to be as per the company guidelines.
The Iridium phone must be tested by calling a number in the company or to the ship’s main satellite phone.
3. Preparedness of the crew to detect and respond to the security threat
The most important part of the HRA transit is the preparedness of the crew.
Before arrival, crew must be trained for their duties during the transit period.
As the ship need to have extra look out posted during HRA transit, a watch schedule must be made and discussed with all crew.
Apart from that, the access points must be discussed during the crew briefing.
During daytime, only one access is allowed for the crew if the crew need to work on deck. This one access must be agreed and controlled by the officer on watch.
All other access points need to be sealed before entering the HRA.
The crew needs to be trained for a citadel drill.
If the company has defined the procedures for citadel drill, that should be followed. If not then a citadel drill plan can be discussed and agreed with all crew.
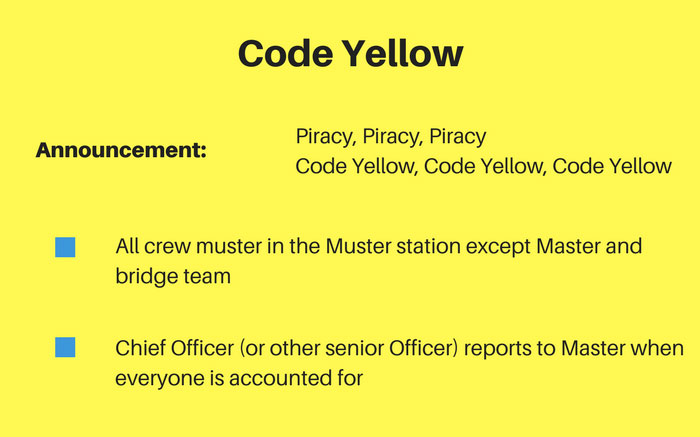
Code yellow, Code Red, Lockdown is one of the most common citadel drill plans.
This plan has three stages.
For Code Yellow, Master then announces “Piracy Piracy Code Red”. This means that the pirate boat is attempting to board the vessel.
With this announcement, all crew members muster at muster station and all persons need to be accounted for.
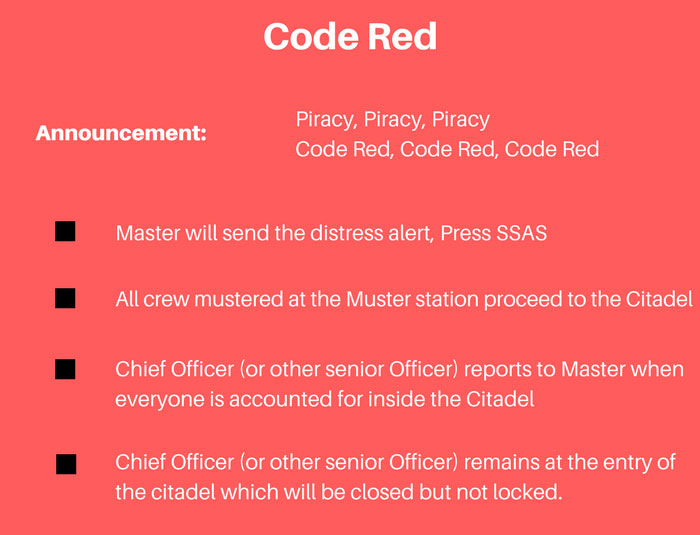
For Code Red, Master then announces “Piracy Piracy Code Red”. This means that the pirate boat is attempting to board the vessel.
With this announcement, all the crew members mustered at the muster station need to proceed to the citadel.
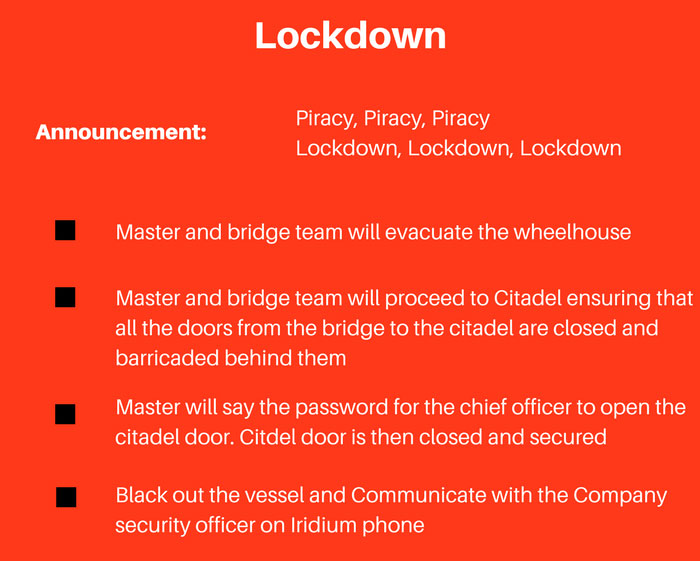
In the last stage, Master then announces “Piracy Piracy Lockdown”. This means that the pirates have succeeded in boarding the vessel and the bridge team is proceeding to the citadel for lockdown.
When the bridge team arrives at the Citadel, they say a pre-agreed password to the crew inside the citadel.
Only upon hearing the correct password the crew inside would open the citadel.
Transiting with Armed Security Guards
Many companies provide armed guards for crossing the high risk area. This is the safest option for the vessel considering the fact that not a single ship with armed guards on board has been boarded by pirates.
When planned to transit with armed guards, vessel must report to the relevant departments.
Vessel may need to divert to pick up the guards before HRA and drop them after the HRA.
In this case, charterers need to be informed well in advance about this diversion.
Mast should check with the company if Hull & machinery underwriters need to be informed about the boarding of armed guards.
In most of the case, H&M underwriters need to be informed about the time, date, position and details of the armed guards boarded.
If it is required, inform the H&M underwriters when armed Guards board the vessel and when they leave the vessel after crossing the HRA.
Security Assessment by Armed guards
Once armed guards board the vessel, they will do a security assessment of the vessel and will advise on any security gaps that may need to be addressed.
They may wish to have the crew briefed about the security and may require to conduct one Citadel security drill.
Under their standard procedures, armed guards need to test fire few bullets. If so, check your company’s procedures if they are allowed to test fire.
Conclusion
Dealing with the piracy has been one of the main challenge for the shipping trade for many years.
Piracy and hijacking in the Somalian waters has increased the stakes many fold.
Security measures highlighted in the “Best management practices 04th edition” reduces these risks significantly.
If the ship and crew are prepared as per these measures chances of pirates succeeding to take control of the vessel would be minimal.
Share this:

About Capt Rajeev Jassal
Capt. Rajeev Jassal has sailed for over 28 years mainly on crude oil, product and chemical tankers. He holds MBA in shipping & Logistics degree from London. He has done extensive research on quantitatively measuring Safety culture onboard and safety climate ashore which he believes is the most important element for safer shipping.
Search Blog
5 Comments


Nice blog Sir

There are many critical benefits to having an Armed Security Guard Services presence for your business, the primary roles for an Armed Security Guard Services are to deter potential threats and to actively respond to immediate threats. Our guards will know exactly how to deal with the threat, using their specialized training and knowledge to act quickly and appropriately. Our armed guards know how to handle a variety of situations with the protection of your people and your property as their number one priority. https://www.centralprotection.ca/
Leave Comment
More things to do on myseatime

MySeaTime Blogs
Learn the difficult concepts of sailing described in a easy and story-telling way. These detailed and well researched articles provides value reading for all ranks.
Seafarers Question Answers
Ask or answer a question on this forum. Knowledge dies if it remains in our head. Share your knowledge by writing answers to the question

MySeaTime Podcast
This podcast on the maritime matters will provide value to the listeners. Short, crisp and full of value. Stay tuned for this section.






Sir, I really appreciate your efforts to give knowledge to us regarding this thing. I have read all your blog and they are very good. But please consider changing this map of India. At least in India show a map which we normally use, not from other countries what they use.
I Appreciate your fine observation Abhishek, I will change that...
Good day Capt. I too am planning to pursue my MBA in shipping and logistics. Wanted to talk to you about it as I am not from sailing background. Please help.